by Vikram Goyal and Darrin VandenBos
By the time you read this article, ZENworks 2020 will be very close to release. Our goal for each release is to enhance your ability to manage and secure your endpoint devices, as environments grow increasingly more complex. ZENworks 2020 builds on this legacy by adding exciting new value in three primary areas:
- Device security
- Bundle status
- Customer-requested enhancements
Device Security
Securing and protecting your organisation’s devices is of utmost importance in today’s environment of ever-increasing cyber-attacks and mobile users. ZENworks 2020 provides key enhancements to device security, allowing you to:
- Manage security under one area in ZENworks Control Center. This includes a video-assisted getting started that helps you quickly learn about and implement the ZENworks security capabilities.
- Identify software security vulnerabilities through the use of Common Vulnerabilities and Exposures (CVE) IDs, track which vulnerabilities impact devices in your zone, and easily remediate vulnerabilities on those devices through one-click application of all patches required for the vulnerability.
- Gain greater insight into patch details such as supersedence and device assignments.
- Encrypt folders on fixed disks.
Easier Accessibility to All-Things Security
ZENworks 2020 includes security capabilities from ZENworks Patch Management, ZENworks Endpoint Security Management, and ZENworks Full Disk Encryption. In previous versions, these capabilities were presented separately in ZENworks Control Center. To provide one-stop access to capabilities that cross all security products, such as dashboards and getting started information, these capabilities have been combined under one security area, as shown in figure 1.
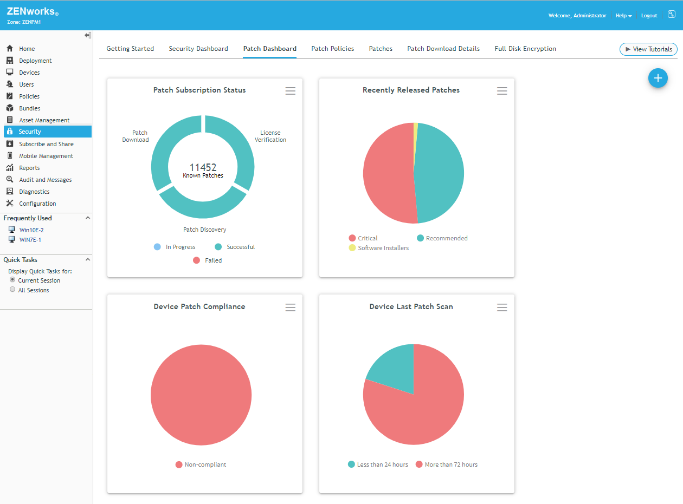
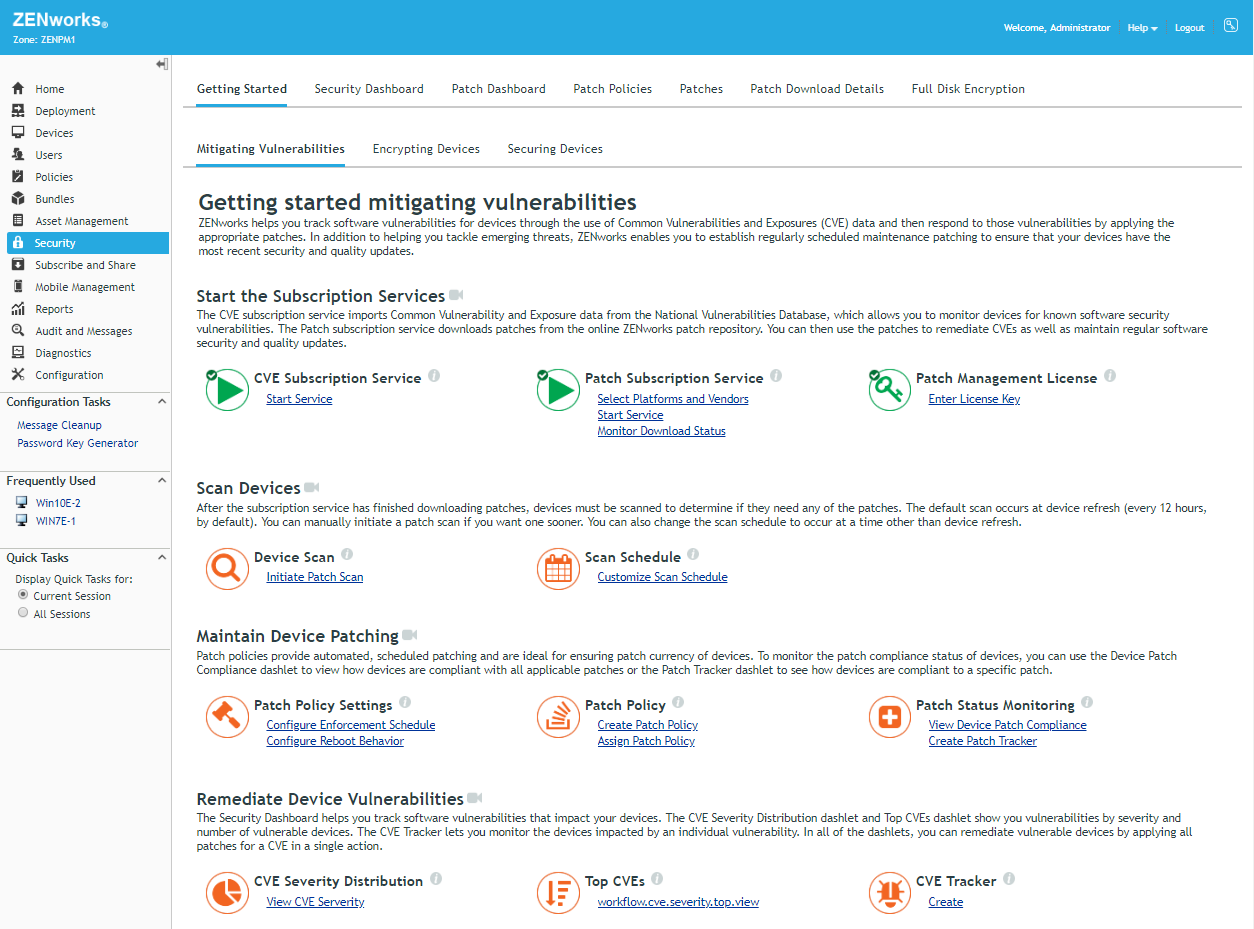
If you aren’t already using all of these security capabilities, the new Security Getting Started enables you to quickly start using them or simply test them out. The Security Getting Started focuses on three areas:
- Mitigating Software Vulnerabilities: This Getting Started helps you configure ZENworks to use CVE data to identify, track, and remediate software vulnerabilities on-demand through ZENworks Patch Management. It also helps you schedule patching through Patch policies to maintain patch currency (Figure 2).
- Encrypting Devices: This Getting Started helps you encrypt a Windows device’s fixed disk volumes, fixed disk folders, and removable data drives.
- Securing Devices: This Getting Started helps you create locations and apply Security policies such as application control, storage control, and Wi-Fi access to Windows devices. It also helps you apply Security policies to mobile devices that let you control passwords, device features, and much more.
Remediating Software Vulnerabilities Based on CVEs
ZENworks 2020 imports CVE data from the NIST National Vulnerability Database. By associating this CVE data with patches made available through ZENworks Patch Management, ZENworks 2020 is able to determine which CVEs apply to devices in your zone.
A new Security dashboard includes two dashlets that show the CVEs that are applicable to your managed devices. The CVE Severity Distribution dashlet groups applicable CVEs by their severity (Critical, High, Medium, Low, or None). The Top CVEs dashlet lets you view applicable CVEs by most recently released, highest severity, or most vulnerable devices. (Figure 3).
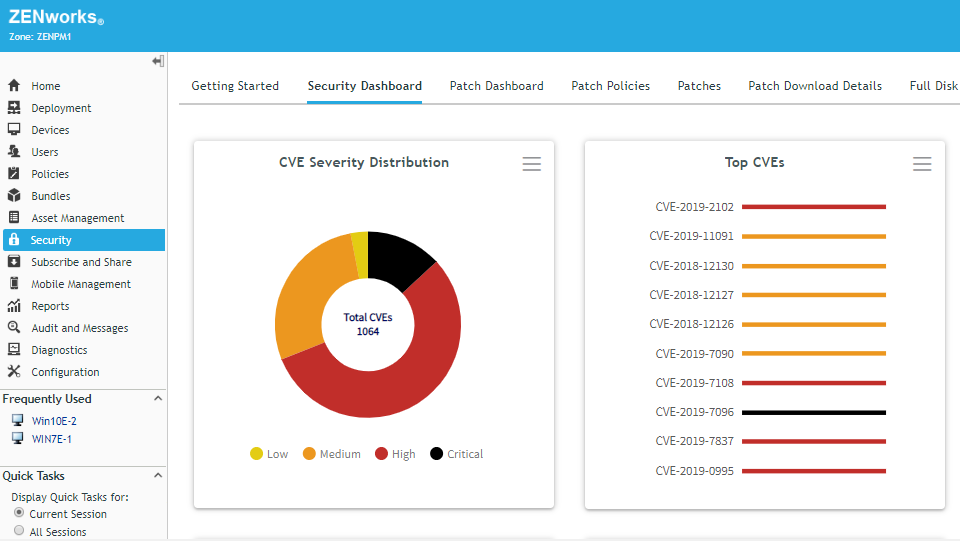
When you expand either of the dashlets, the CVEs are listed along with the number of devices that are vulnerable to each CVE. You can select one or more CVEs that have vulnerable devices and immediately deploy the patches required to remediate the devices.
By default, the dashlets show all CVEs that apply to devices for which you have device rights. You can use the filters to show the CVEs that are applicable to specific device folders or groups and as well as filter on device type (server or workstation), platform, or impacted vendor. You can then save your customised dashlet.
In cases such as critical vulnerabilities like WannaCry or BlueKeep you might want to track an individual CVE to focus more attention on it. The CVE Tracker dashlet gives you the ability to do just this, allowing you to identify a CVE and place a tracking dashlet on the Security dashboard. (Figure 4).
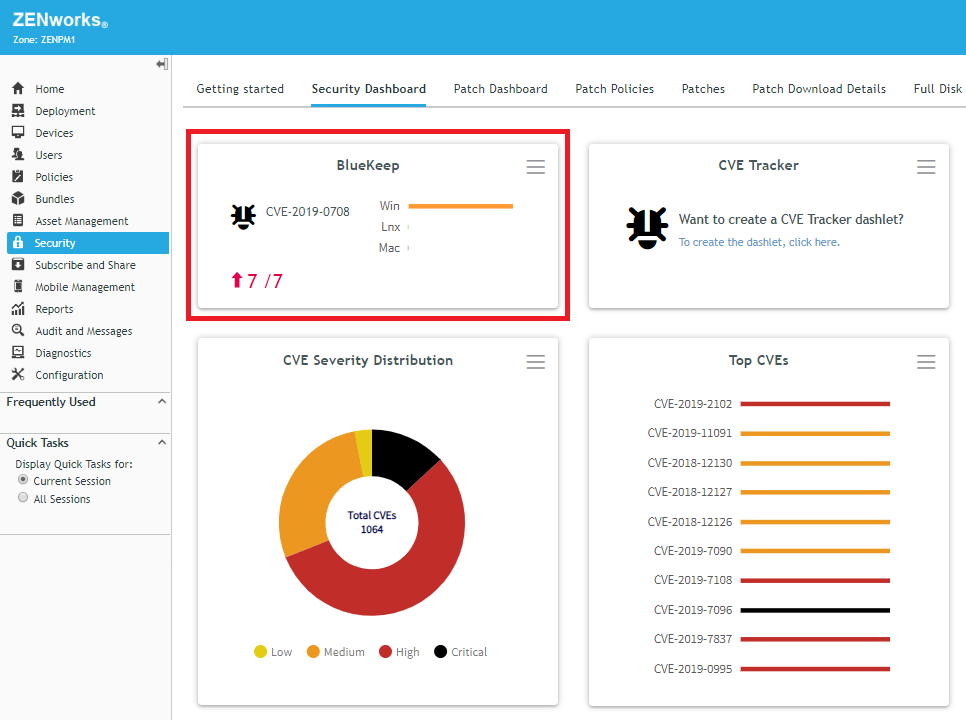
The dashlet shows the total number of devices to which the vulnerability applies and the number that are currently still vulnerable. In the screen shot, this is represented by the red 7/7, where the first number indicates vulnerable devices and the second number indicates total devices. The red up arrow and numbers indicate a rising trend in the number of vulnerable devices. A green down arrow would indicate a declining trend.
You can expand the tracker to see a list of devices that are currently vulnerable as well as view the vulnerability trend over time. And, most importantly, you can select one or more vulnerable devices and immediately deploy the patches required to remediate the devices. (Figure 5).
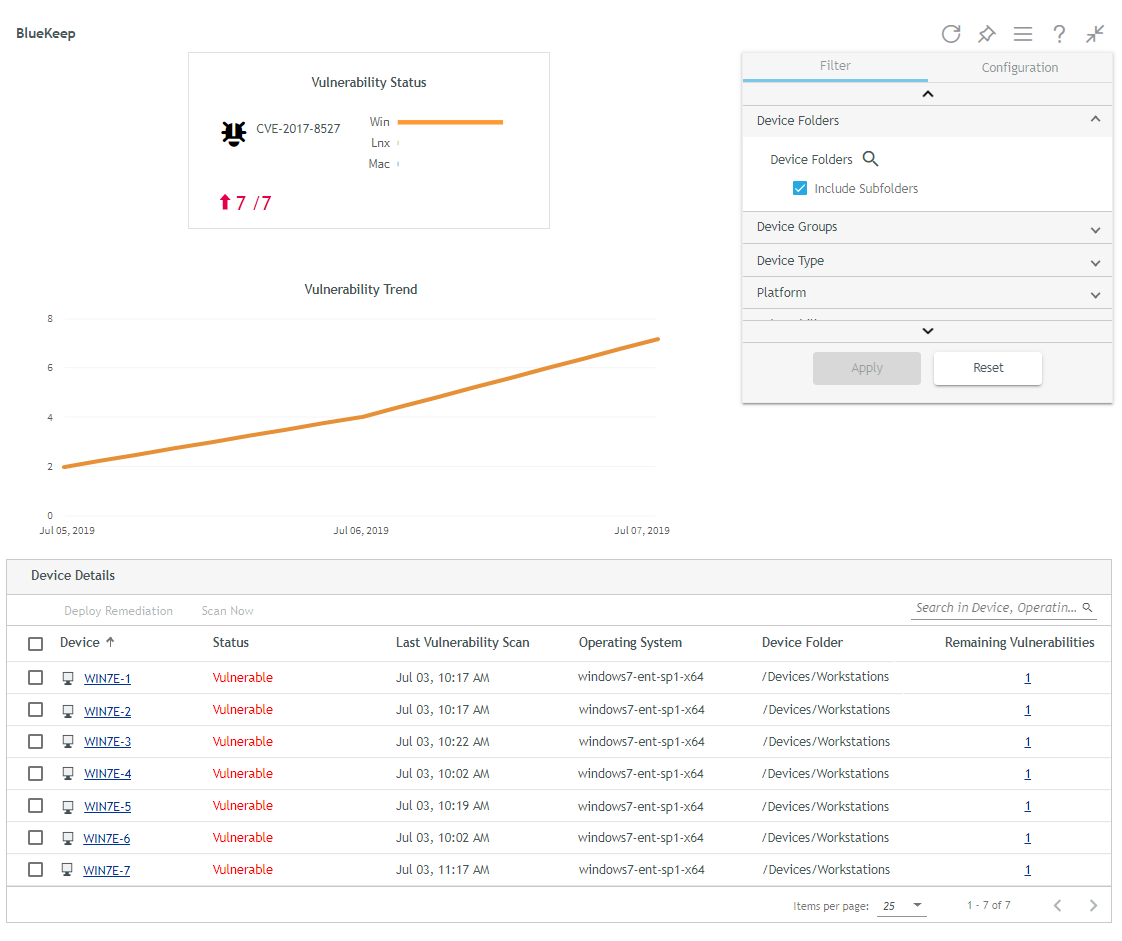
NOTE: Trend data requires the use of the Vertica database included in ZENworks 2020.
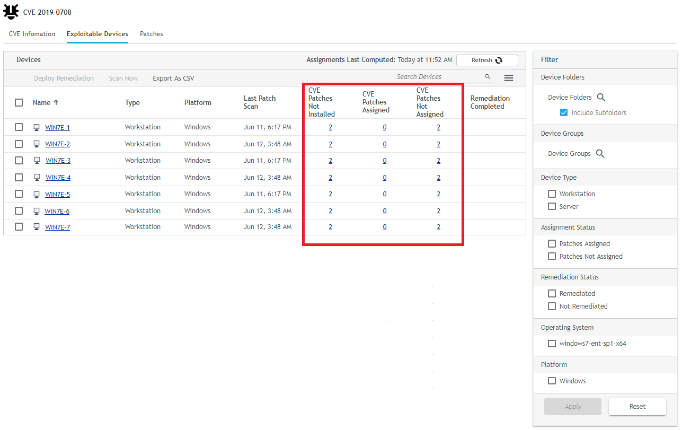
If the dashlet views don’t provide all of the information you want about a vulnerability, you can drill into any CVE to get more details. This includes information provided by the National Vulnerability Database such as the CVE’s score and severity, when it was released and last modified, the vulnerability type, and the list of vulnerable software and version.
You can also see the list of exploitable devices (i.e. the devices to which the CVE is applicable) as well as the list of patches that remediate the CVE. When viewing the list of exploitable devices, you can see which of the CVEs patches are not installed on a device. More importantly, you can see which patches are not assigned to the device. At that point, you can decide if you want to assign the patches via a Patch policy or use a Remediation deployment to immediately patch the device. (Figure 6).
Greater Insight into Patch Details
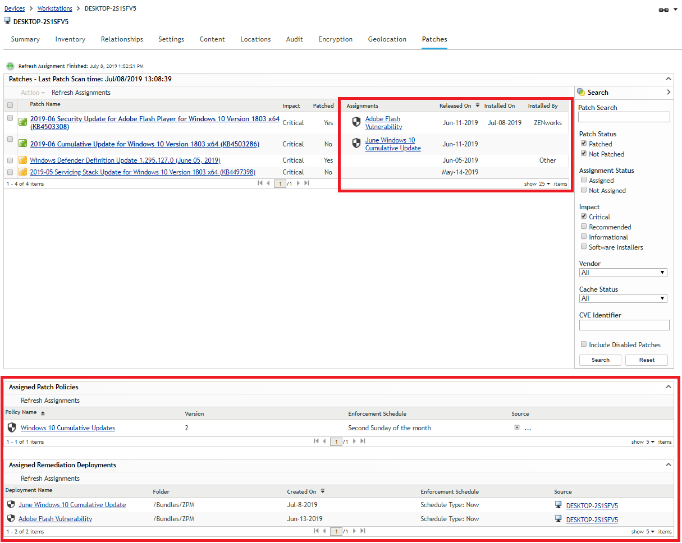
As you’ve hopefully seen by now, ZENworks 2020 is focused on making it easier for you to see what is going on with your devices from a security perspective and then taking action to make them more secure. To that end we’ve greatly increased the information available when viewing patch details (Figure 7).
For an enabled patch, you can now see the patches that it supersedes. For disabled patches you can see the patches that supersede it. Add to that the fact that disabled patches now retain their patched device information and you have better ability, if necessary, to drill into a patch and trace whether or not it or an equally suitable patch has been applied to remediate a vulnerability on devices.
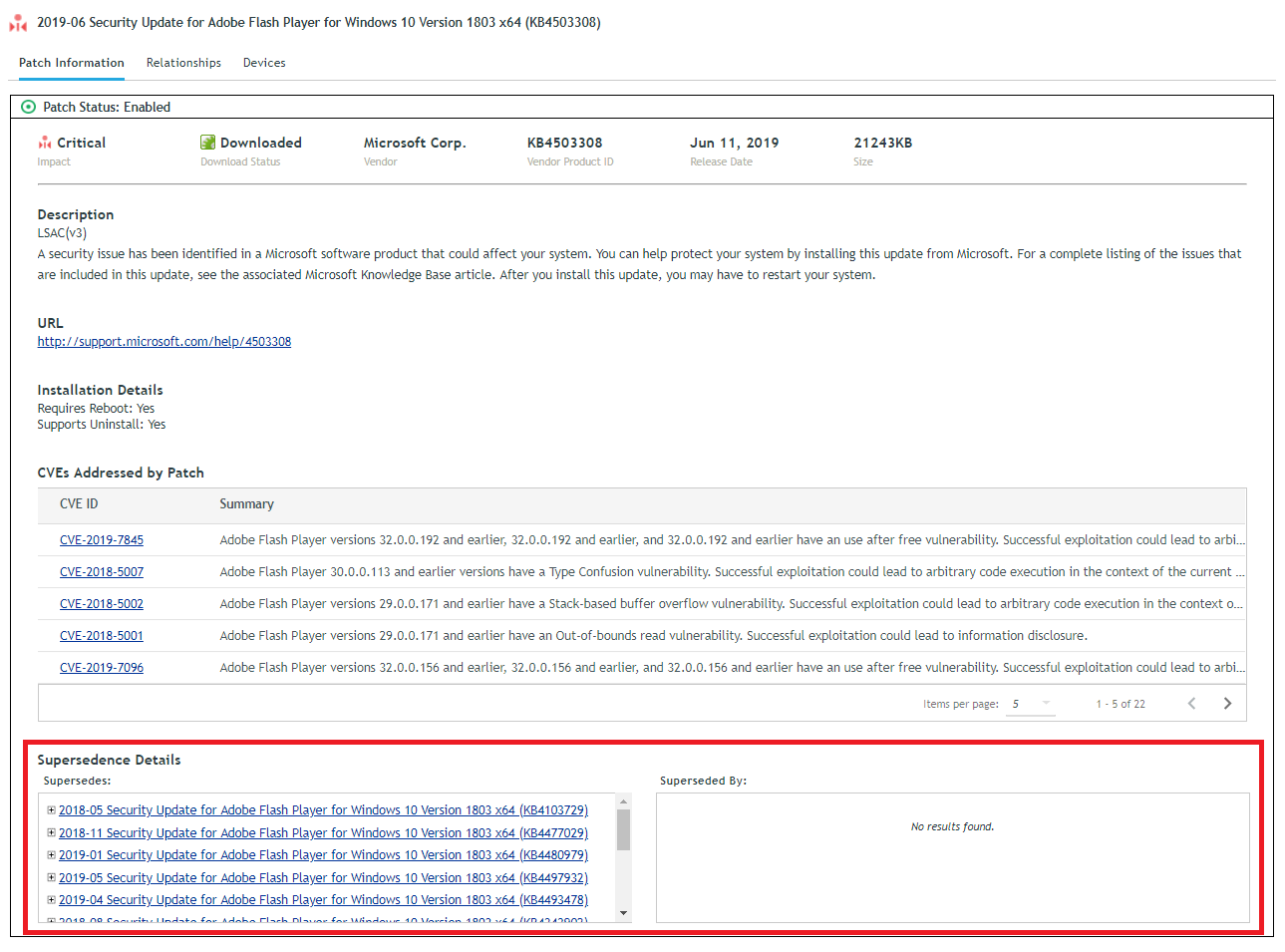
In addition, the patch details include a list of devices to which the patch is applicable, whether or not the patch is installed on the device, and if it is assigned to the device either through a Patch policy or a Remediation deployment. If the patch is installed, you can see when it was installed on the device and whether ZENworks or another program installed it.
The patch information for individual devices has also been greatly enhanced. For each patch that is applicable to the device, you can see if the patch has been assigned to the device through a Patch policy or Remediation deployment. For installed patches, you can see the installation date and the patch agent (either ZENworks or Other). Finally, you can also see a list of all Patch policies and Remediation deployments assigned to the device. (Figure 8).
Encryption of Fixed-Disk Folders
ZENworks 2020 introduces the ability to encrypt folders on Windows fixed disks. This supplements the existing capabilities that enable you to encrypt entire fixed disk volumes and removable data drives.
Fixed-disk folder encryption uses the native Microsoft Encrypted File System (EFS) while adding capabilities that make it more secure and easier to use. You enable and disable the fixed-disk folder encryption through the existing Microsoft Data Encryption policy. This policy is available in ZENworks Endpoint Security Management and already provides removable data drive encryption (via Bitlocker), as shown in figure 9.
As an administrator, you define the folders in policy that you want encrypted on devices where the policy is applied. Folder paths can include system variables such as %userprofile% to ensure that you can enforce encryption across a variety of user environments. Once a policy is applied to a device, its user can also specify additional folders to encrypt.
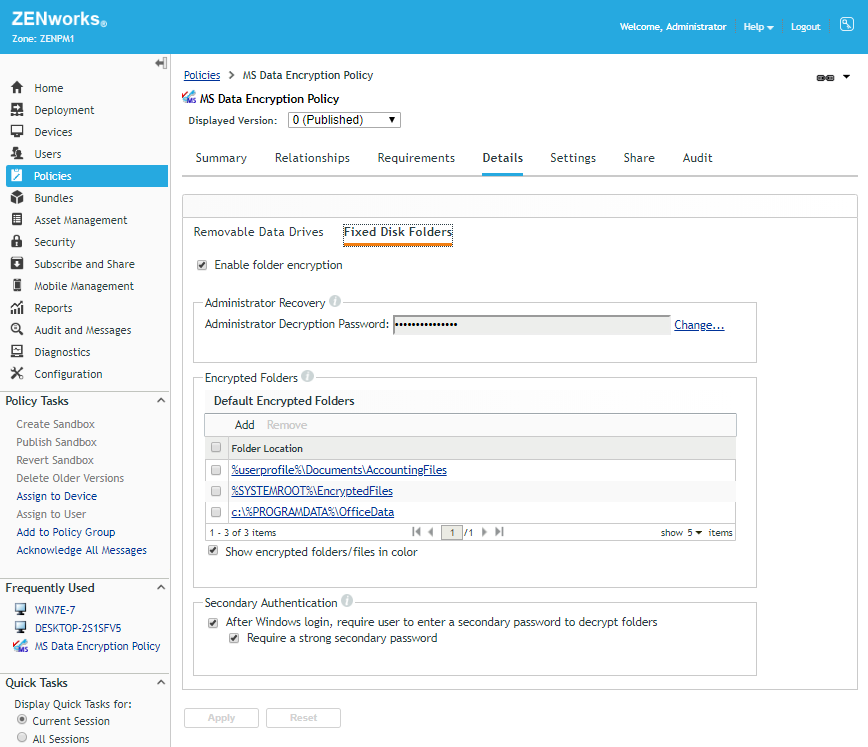
ZENworks 2020 adds to the above-mentioned standard EFS capabilities with this enhanced functionality:
- Secondary Authentication: Normally, EFS-encrypted folders are available once a user logs in to Windows. You can enable secondary authentication to enforce an additional layer of security. With secondary authentication, the user must enter a second password before any encrypted folders can be accessed. This second password is defined by the user and can include a password hint to help if the password is forgotten.
- Administrator Recovery: If both the user’s memory and the password hint fail, an administrator recovery password enables recovery of files from encrypted folders when the Microsoft Data Encryption policy is still applied. In addition, storage of the EFS certificate on the ZENworks server ensures that encrypted folders can be decrypted in emergency scenarios where the policy has been removed but the folders remain encrypted.
- Multi-User Support: Multiple users can share the same device with a combination of private encrypted folders and shared encrypted folders. Any policy-defined encrypted folders within the %userprofile% context are private whereas any policy-defined encrypted folders outside the %userprofile% context are shared, meaning the files in the encrypted folders are available to all users who log in on the device. Folders encrypted by users are always private.
Bundle Status
We know that the ZENworks ability to deliver applications using bundles is one of our most liked and used capabilities. Unfortunately, in previous ZENworks versions there are cases where bundle status may not have been current or even accurate. Because it is so important for you to know the exact status of an application, we’ve essentially done a ground-up rebuild of bundle status in ZENworks 2020.
More Accurate Bundle Status
The revamped bundle status includes the following improvements:
- More Current Status: In a large zone having many satellites, bundle status generally reaches a ZENworks Primary Server (and the ZENworks database) by passing through satellites. This can potentially cause delay in the upload of status. In ZENworks 2020, every device now sends bundle status directly to a ZENworks Primary Server. This means that bundle status is more current. To conserve bandwidth, we have ensured that status data is highly compressed. We have also introduced a quick task that fetches the status of a bundle for selected devices, which means it is possible to get an almost real-time view of what is happening on a device.
- Version Specific Status: When a newer version of a bundle is published, distribution to a device can take some time depending on various factors. This means that the bundle on the device might not be the same version as the published version in ZENworks Control Center, resulting in incorrect bundle status. To resolve this issue, ZENworks 2020 introduces versioning for bundle status as well as version-specific status for Distribution, Install, and Launch. With this, it is now possible to identify the version which was distributed, installed and launched along with the respective status.
- Automatic Reconciliation of Status: In ZENworks 2020, we are also taking care to reconcile status when a device is re-imaged, the cache is cleared, and so on so that status is always accurate and up to date.
- Child Bundle Status: Previously, when a bundle included child bundles, only the status for the parent bundle was reported. ZENworks 2020 now reports status for child bundles as well.
Bundle Status Dashboard
With status being more accurate, we wanted to introduce an easier and more understandable way to view status. ZENworks 2020 takes advantage of our Actionable Dashboard framework to provide a visual representation of a bundle’s status. Every bundle has a dashboard that displays dashlets corresponding to Assignment and Deployment status., as shown in figure 10.
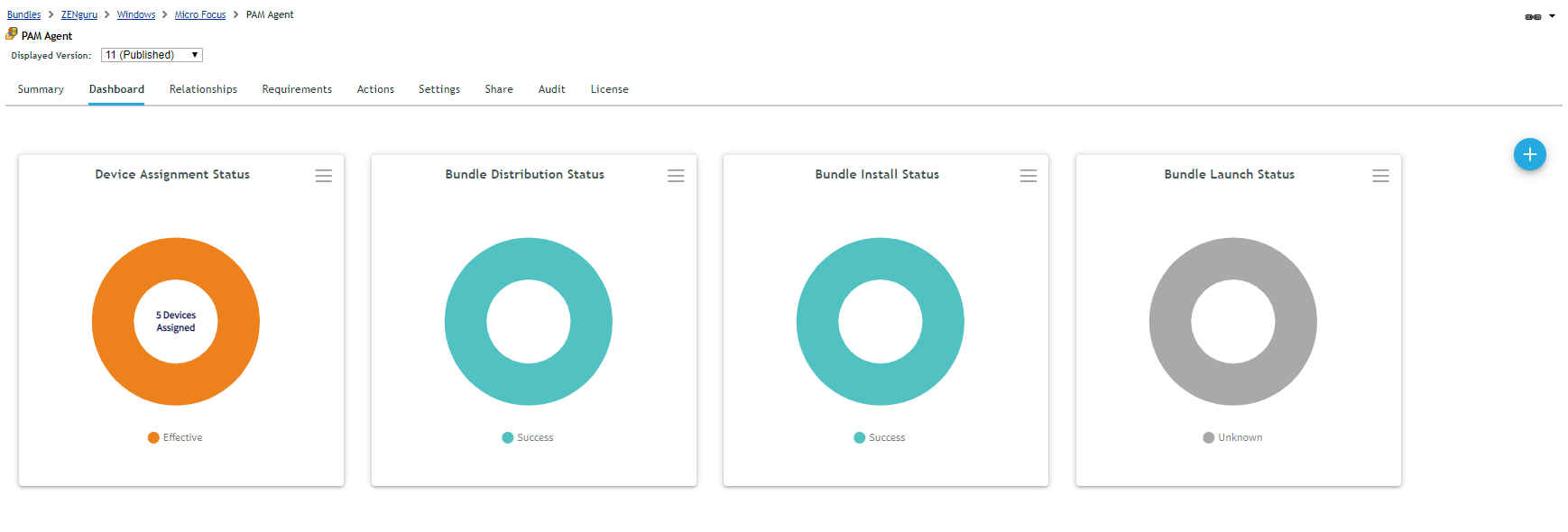
Assignment Status Dashlets
ZENworks 2020 introduces two default dashlets that track the device and user assignment status for a bundle.
Using these dashlets, it is very easy to identify how many devices and users a bundle is assigned to, along with the status of the assignment.
Deployment Dashlets
ZENworks 2020 also introduces three default dashlets to track distribution, install, and launch status of a bundle. Using these dashlets, you can now get answers to important questions regarding the status of a bundle, including:
On which devices the bundle is failing
The reason for the failure
Which devices have the bundle installed even though it is no longer assigned to them
On which devices the bundle was distributed but never got installed
Deployment dashlets have over 20 filters, ranging across devices, users, status, time range, and more, so that you can create a status dashlet meeting very specific needs.
Customer-Requested Enhancements
ZENworks 2020 delivers many enhancements that you, our customers, have requested. Here are a few of the highly-requested:
- Apply Patches on Shutdown: This is one of the top requests in the Ideas portal so we are really happy to announce that this is in ZENworks 2020. Now it is possible to schedule patches to be applied when a device is shut down. In the next release, we plan to bring in the same ability for bundles.
- Initiate a Patch Scan: You can now initiate a patch scan on a device via a ZENworks Control Center quick task. The quick task lets you choose whether to use the device’s existing scan file (DAU), download the current one from the ZENworks server, or just upload the last scan results from the device.
- Install Executable Action: This is another one of the top ideas in the Ideas portal. Currently, when installing content you first define an action to download the content to a folder on a device and then execute it; post execution you have to make sure to clean up the downloaded content. The Install Executable action combines everything in one so that when a bundle is executed its content is downloaded into cache and then executed from there. This results in more efficient bundle management, using less disk space on the device and avoiding the need to manage the file deletion.
- Deletion of Older Bundle/Policy Versions: Managing older bundle and policy versions can be very challenging, especially with each version taking up space in the system. ZENworks 2020 allows you to specify how many old versions of a bundle or policy to retain, either all, none, or a specified number. Like other ZENworks configuration settings, you can define this setting at the Zone, folder, or individual bundle/ policy level.
Dropping Sybase as a Supported Database Platform
In ZENworks 2020, we are dropping Sybase as a supported database platform. This means that ZENworks will now only support the following three databases: PostgreSQL, MS SQL and Oracle.
Dropping Sybase helps us focus more on scaling up PostgreSQL so that eventually it can serve as a viable alternative to MS SQL and Oracle. In order to help customers using Sybase, we have already released a database migration utility for Sybase to PostgreSQL that can be used before upgrading to ZENworks 2020. The utility is also built into the ZENworks 2020 upgrade installer.
ZENworks 2020 Has So Much More!
We hope you’ve enjoyed this brief glimpse at the exciting new value being delivered in ZENworks 2020. As you dig in and learn more, we are sure you’ll quickly discover that ZENworks 2020 has many additional enhancements and new features across every area of the product, offering something for every ZENworks administrator to smile and cheer about!
This article was first published in OH Magazine Issue 44, 2019.2, p5-9.