The integration of security and identity in NetIQ Identity Tracking for Identity Manager (ITIM) is unique in the IT world. Identity Tracking is the only product on the market that seamlessly integrates identity management with security event monitoring into a single offering. ITIM connects to Identity Manager (IM) and provides transparency into what users are doing with their access. The ITIM correlation engine monitors and records all user activities in the systems that IM provisions and evaluates them against the policies that you define.
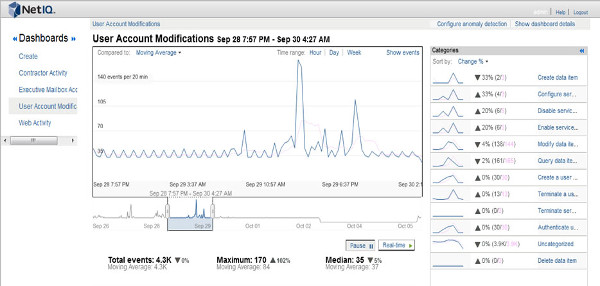
All access logs are tied to the identity information in IM so that you have a clear picture of who does what and can take corrective action if required. If suspicious activity is detected it can send real time notifications and take automated actions – before serious damage or data theft occurs. ITIM can reduce the risks of non-compliant or malicious behaviour which cause failed audits and may lead to fines and damage the reputation of the organisation.
The key differentiators of ITIM are its real time remediation and identity linked event monitoring. Some applications can only monitor and report on user activity but ITIM provides automated, real-time actions in addition, because user identities are directly tied to system activities.
ITIM is supplied with numerous connectors and collectors for commonly provisioned systems, It’s open architecture allows third party connectors to be incorporated.
Besides preventing potentially harmful activity in real time, Identity Tracking also paints a detailed picture of all users for improved decision making. With Identity Tracking, you can:
- Map multiple system entitlements back to a specific user
- See a complete view of a user’s privileges in key systems
- Make informed decisions about provisioning and access requests
You’ll never have to worry about multiple identities for a single user or enforcing critical requirements such as separation of duties.
Identity Tracking is flexible and business driven. It does not lock you in to predefined policies. It’s a straightforward task to adapt your business policies to meet the needs of your unique IT landscape, changing regulations or market opportunities.
ITIM provides comprehensive reporting. Out of the box reports provide insight into provisioning and user activity and for ease of use you can schedule and automatically distribute many reports. Of course you can also write your own custom reports, specifying criteria such as users, time frames and types of activity. These reports help you to enforce company policies and remain compliant with industry and government regulatory requirements.
ITIM runs on SLES 11 SP1 or RHEL6 on its own server or virtualised (minimum VMWare ESX4.0, Hyper-V 2008 server R2 or XEN 4.0). As mentioned it also requires NetIQ Identity Manager v4 to be running. Remember that IM 4 won the SC Magazine Readers Trust Award for Best Identity Management Solution in 2014.
This article first appeared in OH Magazine, Issue 32, January 2016

