Are You Governing Who Has Access To What Effectively?
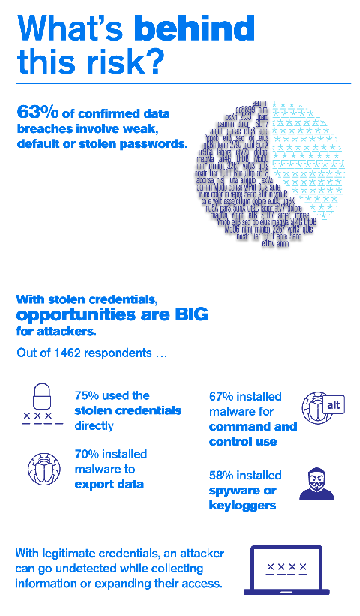
Satisfying identity governance regulations and managing risk requires organizations to inventory, analyze and manage their workers’ access privileges. Failure to manage users’ access to sensitive resources places companies at increased risk for audit findings, fraud or data breaches.
 Access review and recertification campaigns are an essential part of an overall identity governance program. Yet answering the critical question “who has access to what?” is a challenge. Emerging technologies such as mobile devices, cloud computing and social media, combined with shifting workforce trends including growing numbers of contractors, partners and service providers is causing organizations to seek more efficient ways to conduct access certification campaigns that encourage participation by line of business (LOB) managers.
Access review and recertification campaigns are an essential part of an overall identity governance program. Yet answering the critical question “who has access to what?” is a challenge. Emerging technologies such as mobile devices, cloud computing and social media, combined with shifting workforce trends including growing numbers of contractors, partners and service providers is causing organizations to seek more efficient ways to conduct access certification campaigns that encourage participation by line of business (LOB) managers.
Product Overview
Micro Focus’ identity governance product, currently known as Access Review is a platform that helps you run effective access certification campaigns and implement identity governance controls to meet compliance mandates while proactively mitigating risk. It replaces error-prone, time-consuming manual methods that can expose your organization to compliance violations and risk from excessive access.
Access Review provides a way to quickly identify and revoke access to resources users don’t need—such as when users change positions in a company and inadvertently accrue too many privileges. Micro Focus Access Review collects user entitlement information across multiple systems, applications, and data into a consolidated view. This allows IT to provide easy-to-understand reports for LOB managers to validate whether worker access privileges are appropriate and initiate immediate action to revoke access, if necessary.
Key Capabilities
- Collect and review entitlement data across your enterprise, including on-premises and cloud applications, so you have accurate visibility into who has access to what resources.
- Conduct access certifications with campaigns that stay on schedule through automatic reminders and progress updates, including issue escalation for administrators.
- Support decision-making with context that enables LOB managers to make informed decisions about user access.
- Define controls to detect and handle violations and exceptions such as SOD violations or orphan accounts to reduce risk and the most common audit findings.
- Build standard role and attribute authorization models to reduce the scope and duration of access certifications and access request and approval processes. Allows a focus on exceptions, rather than all entitlements.
- Close the loop on remediation, including integration with service desk solutions such as ServiceNow or Remedy for automated ticketing, or automated fulfillment via integration with Micro Focus Identity Manager.
- Conduct reviews prioritised by risk scoring based on attribute value, group membership, management relationship, application, permission, cost, risk and other criteria, providing focus where most needed.
- Report on identity governance with out-of-the-box support for scheduling and distribution that includes entitlements, certification status, request and approvals, and policy violations to make audit reporting easier.
Why do you need Access Review?
Access Review brings rigour to the review process in that it:
- Enforces the principle of least privilege – users should only have the access rights that are essential to their work. This is mandated by security best practices and many compliance regulations.
- Reduces and eliminates entitlement inertia. People change jobs but often retain access rights that are no longer necessary or they leave the company entirely but their accounts may not be closed.
- Detects unused and orphaned accounts
- Detect and remediate policy violations
In combination with Identity Manager access and provisioning control management is extended and enhanced.
The access review process must ideally be identity centric, comprehensive but simple to use and involve the business. The process needs to determine what users access, decide if the access is appropriate and remove unnecessary/inappropriate access.
Access Review uses a workflow type approach. Each Review has a Review owner who manages the process and there are specified reviewers who may be supervisors or managers in the business who are the application owners. The review will also specify an optional auditor who has sign-off responsibilities over the final review. Access Review sends notifications and escalations to the reviewers throughout the process to maintain a timely review.
System Requirements
Access Review is a web based Tomcat application running on SLES with a PostgreSQL or Oracle database back-end for the catalog – which contains the user, application and their permissions and accounts data. It is fully integrated with Micro Focus Identity Manager but has no dependency on it.
Data can be collected via LDAP (from Active Directory or eDirectory for example), JDBC, CSV or directly from Identity Manager. Target applications may be HR systems, AD, CRM and financial systems. Automated fulfillment is provided through those apps managed by IDM, other changes and updates are manual.
This article was first published in OH Magazone Issue 36, 2017/1, p22-23